G Wireless Network Configuration for Security Systems: Essentials for a Safe and Secure Network
As security systems become increasingly dependent on wireless networks, securing these connections is more crucial than ever. A G wireless network configuration for security systems must take into account the specific needs and vulnerabilities of these networks.
Configuring Host-Based Security Tools
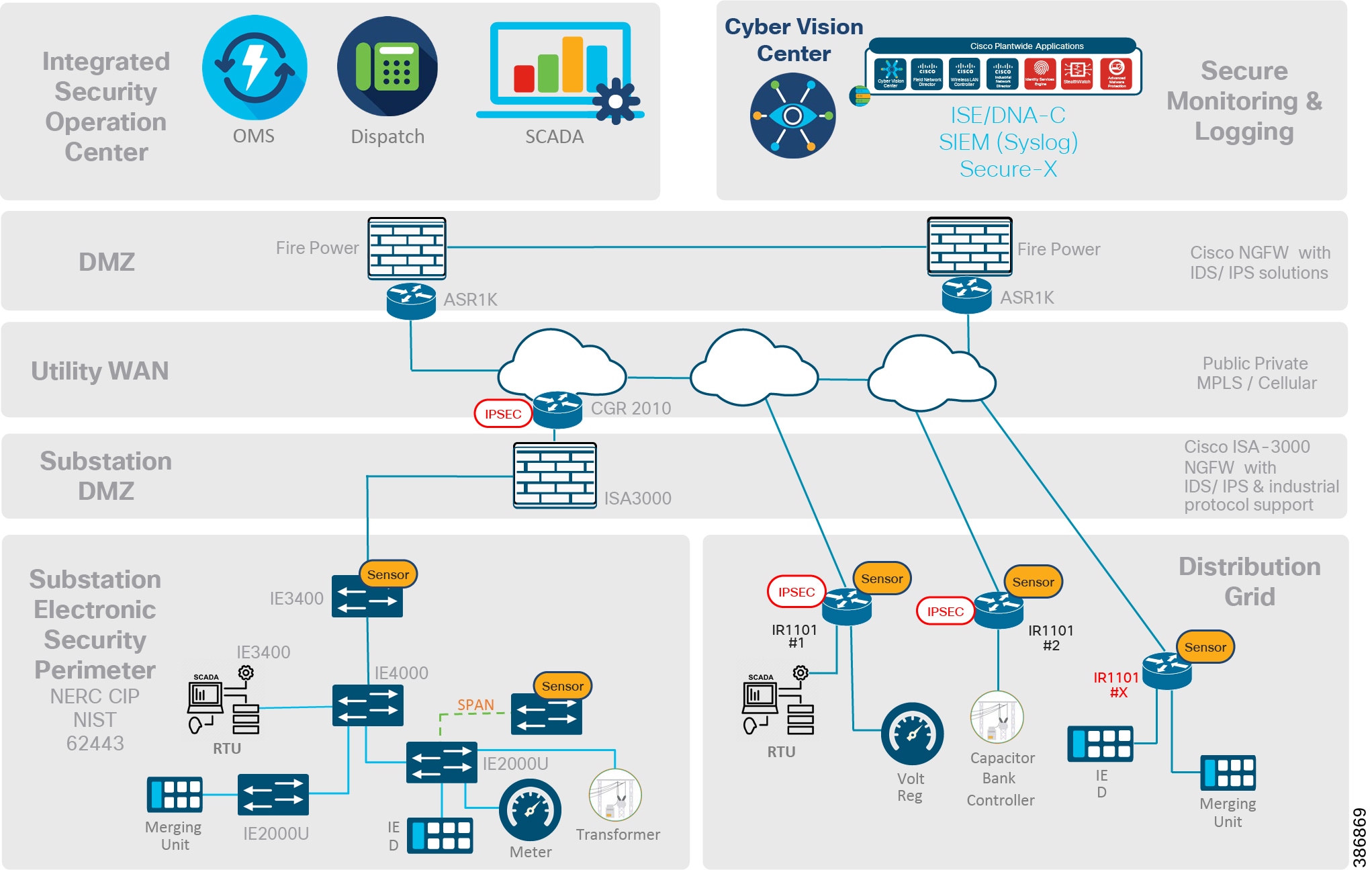
One of the essential steps in securing a G wireless network configuration for security systems is configuring host-based security tools, such as host-based firewalls and host-based intrusion detection and prevention systems (HIDS/HIPS). These tools can help prevent multiple network interfaces from being used at one time, thus reducing the risk of unauthorized access.
Best Practices for Securing Wireless Networks
Securing a wireless network requires attention to several critical factors. Here are the top 12 best practices to ensure your data and devices are safe from malicious actors:
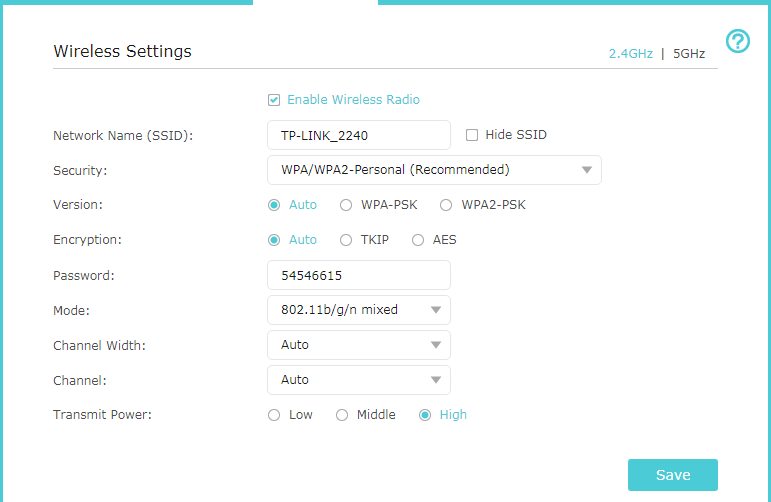
- Secure the network through strong passwords and WPA2 encryption.
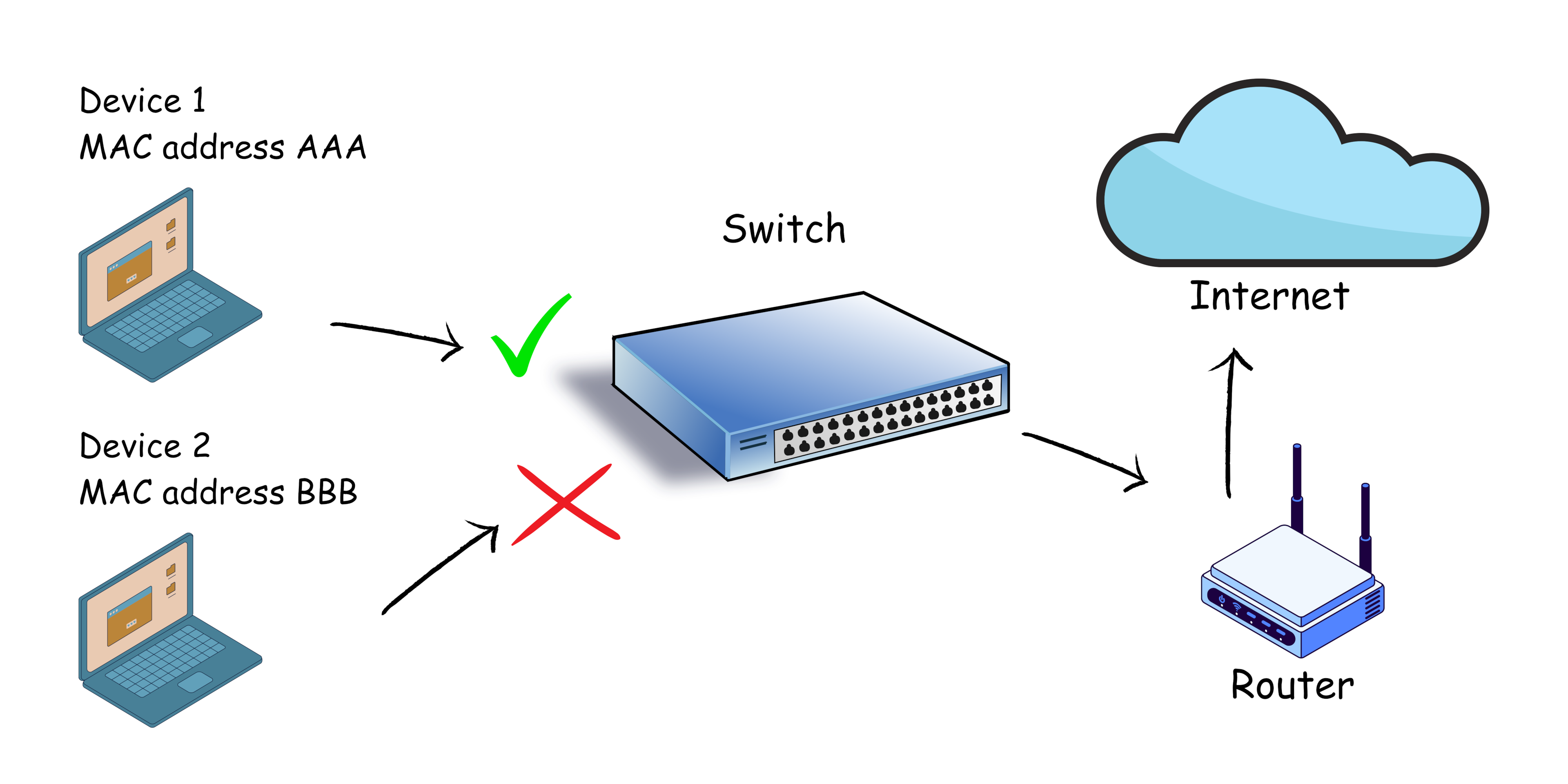
- Limit access to authorized devices only.
- Regularly update firmware and software.
- Monitor network activity and logs.
- Implement a guest network for visitors.
- Use a reputable and secure router.
- Use a VPN for remote access.
- Secure IoT devices.
- Use wireless intrusion detection and prevention systems.
- Regularly perform site surveys and coverage analysis.
- Implement a wireless security policy.
- Provide user education and training.