G Network Configuration for Network Access Control
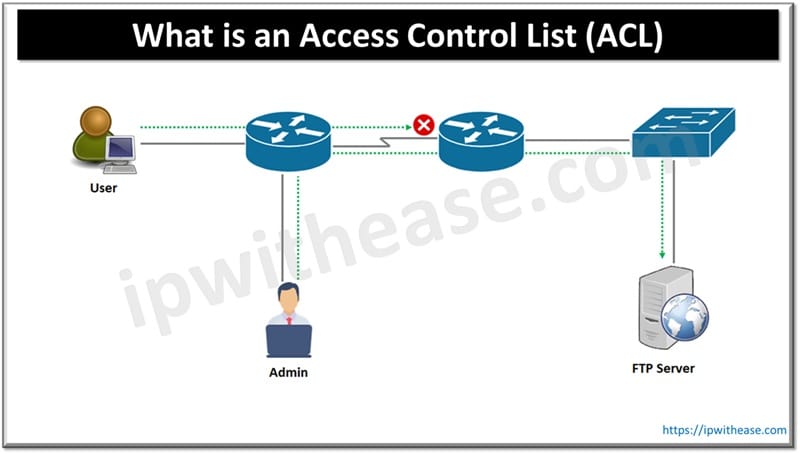
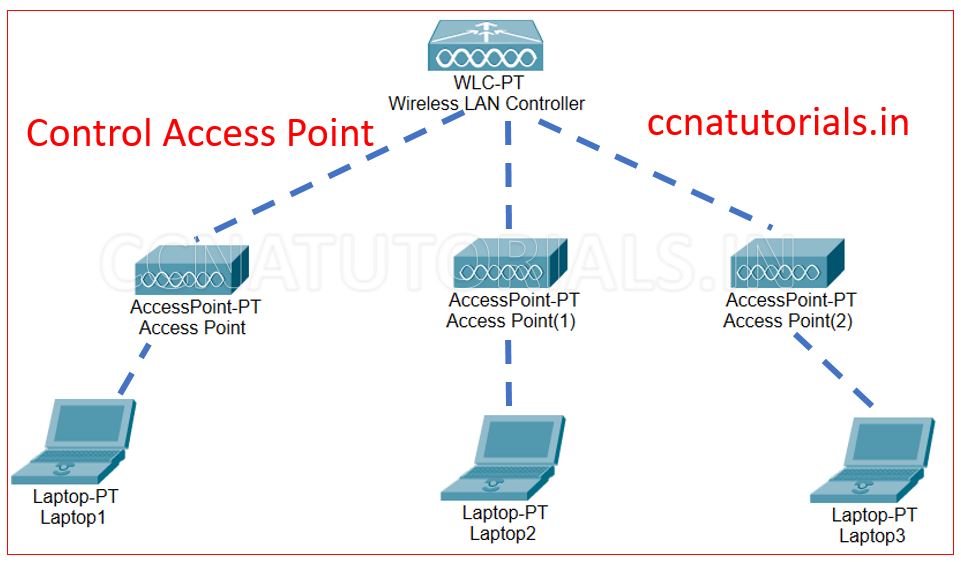
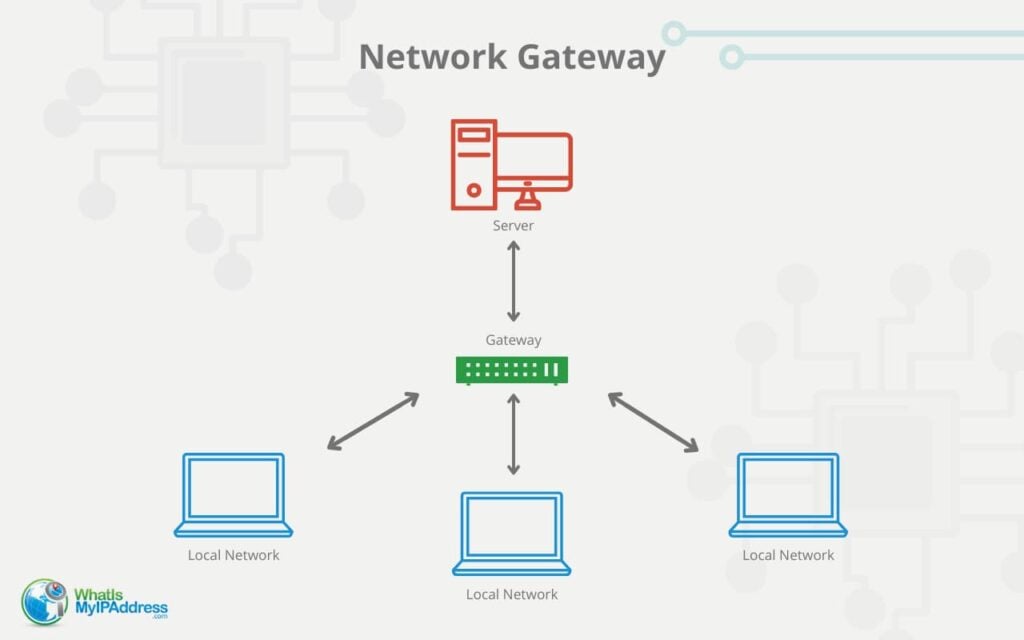
Network access control (NAC) is a security feature that allows network administrators to monitor and record the sessions registered on the GWN78xx, giving a broader image of the type of devices connected to the network through the GWN78xx network switch and allowing only those that can authenticate with a radius server. This type of authentication is called port-based.
Overview of Network Access Control
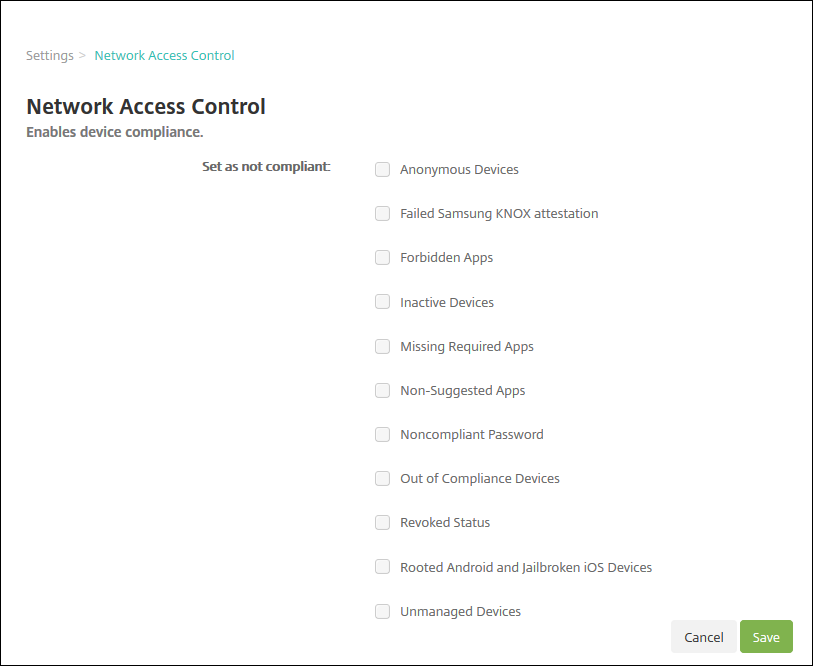
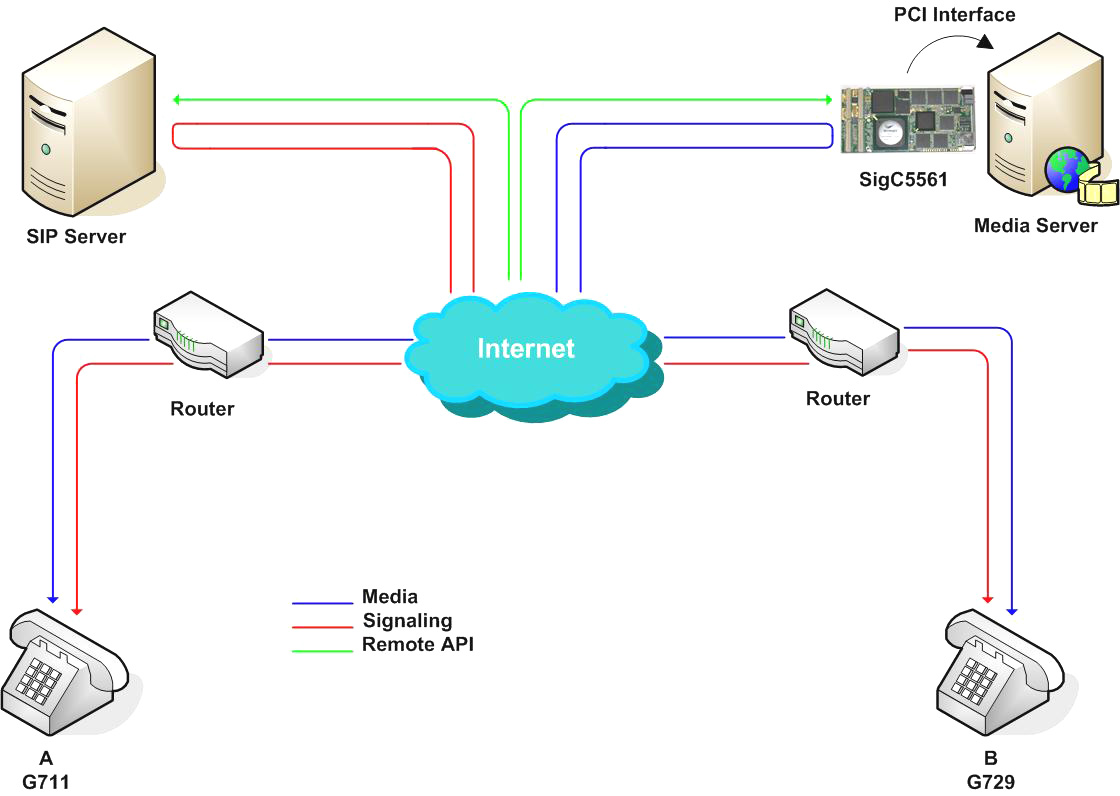
Network access control (NAC) is a security solution that enforces policy on devices that access networks to increase network visibility and reduce risk. It is a critical component in security architecture that manages and enforces access policies for devices connecting to a network. NAC solutions are essential to protect networks from unauthorized devices or users.
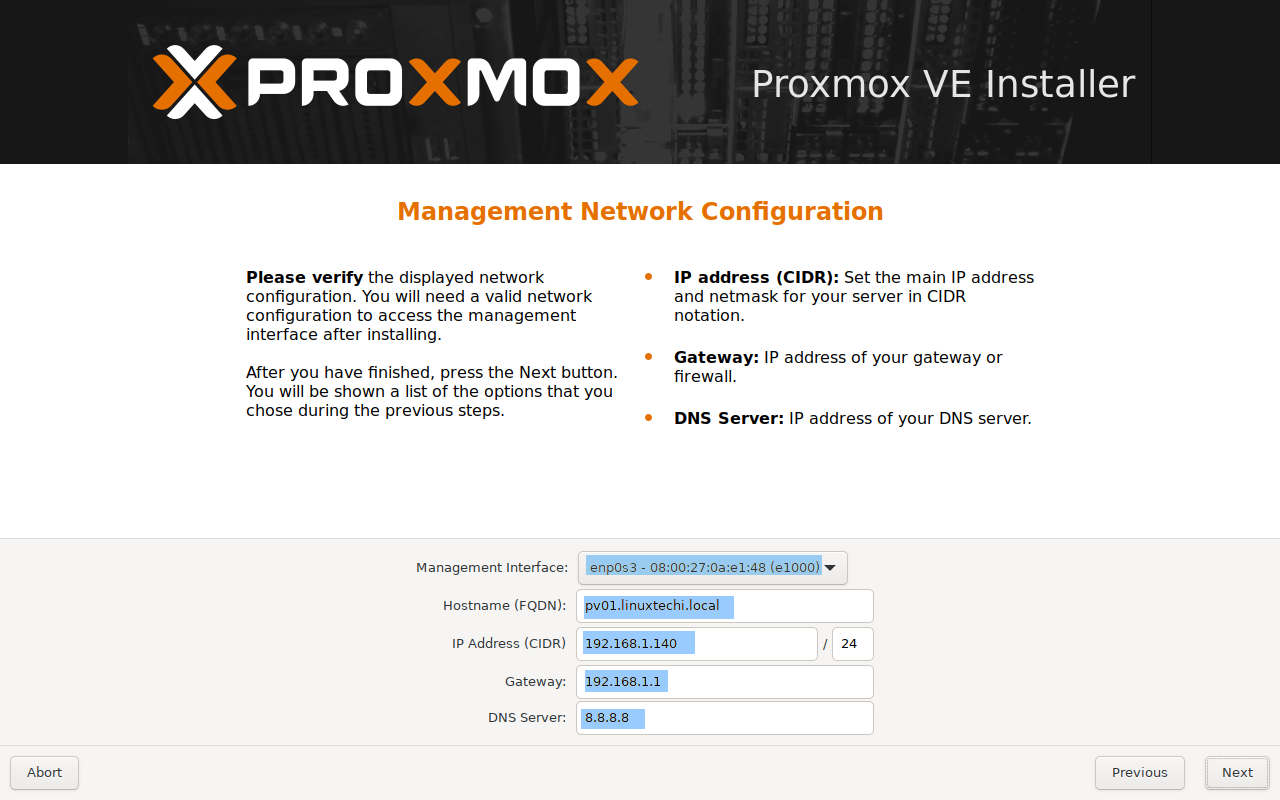
Configuring G Network for NAC
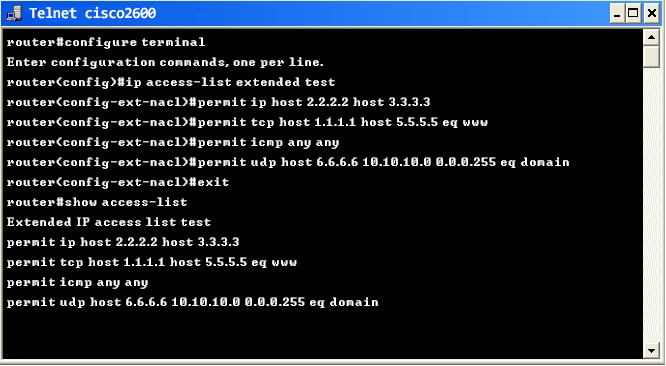
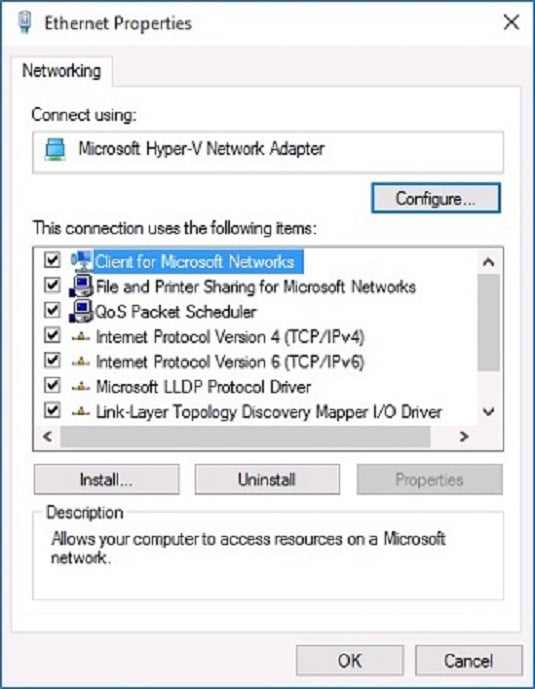
The network switch configuration is identical to the IDevID setup. Refer to the "Configure network switch and switch port for 802.1X use" section in the previous LDevID example for configuration steps.
Network Admission Control (NAC) Features
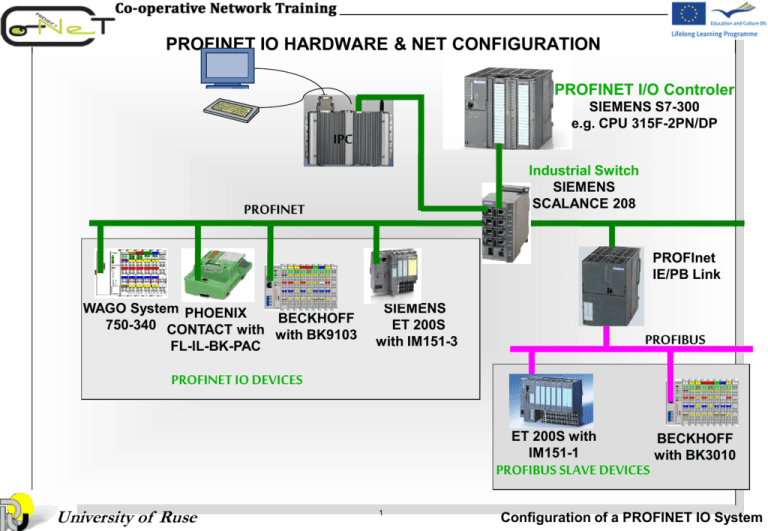
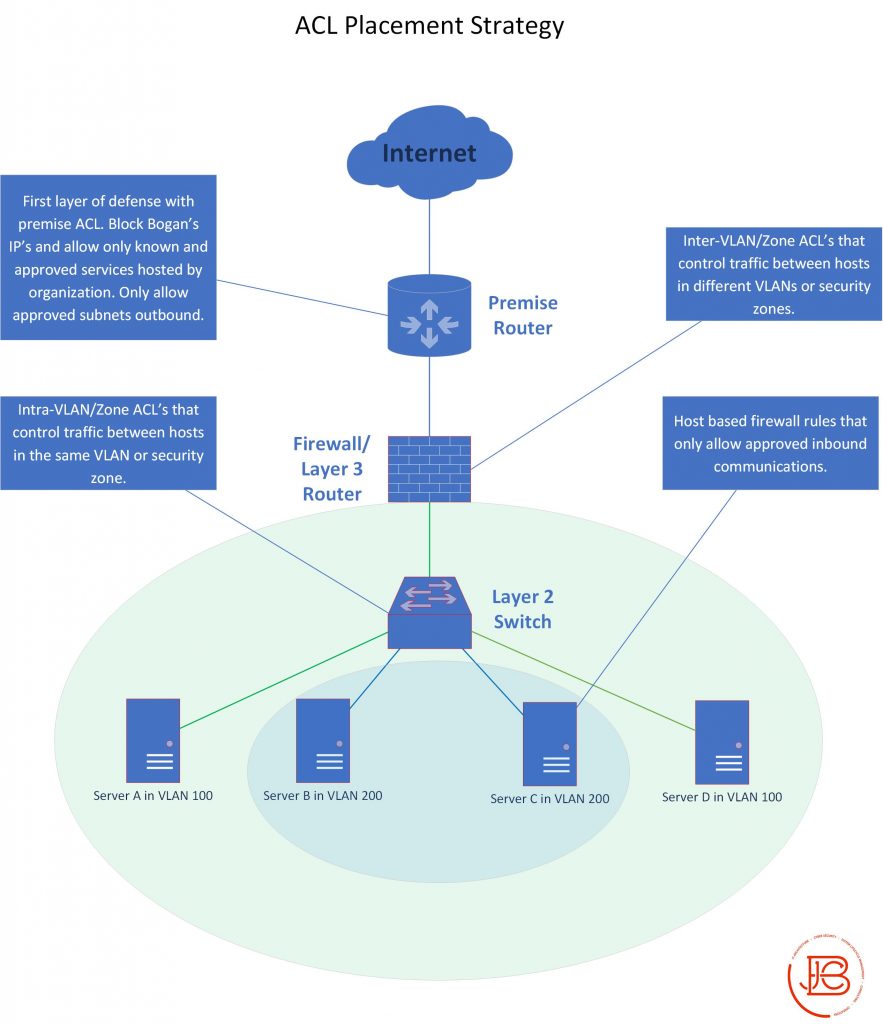
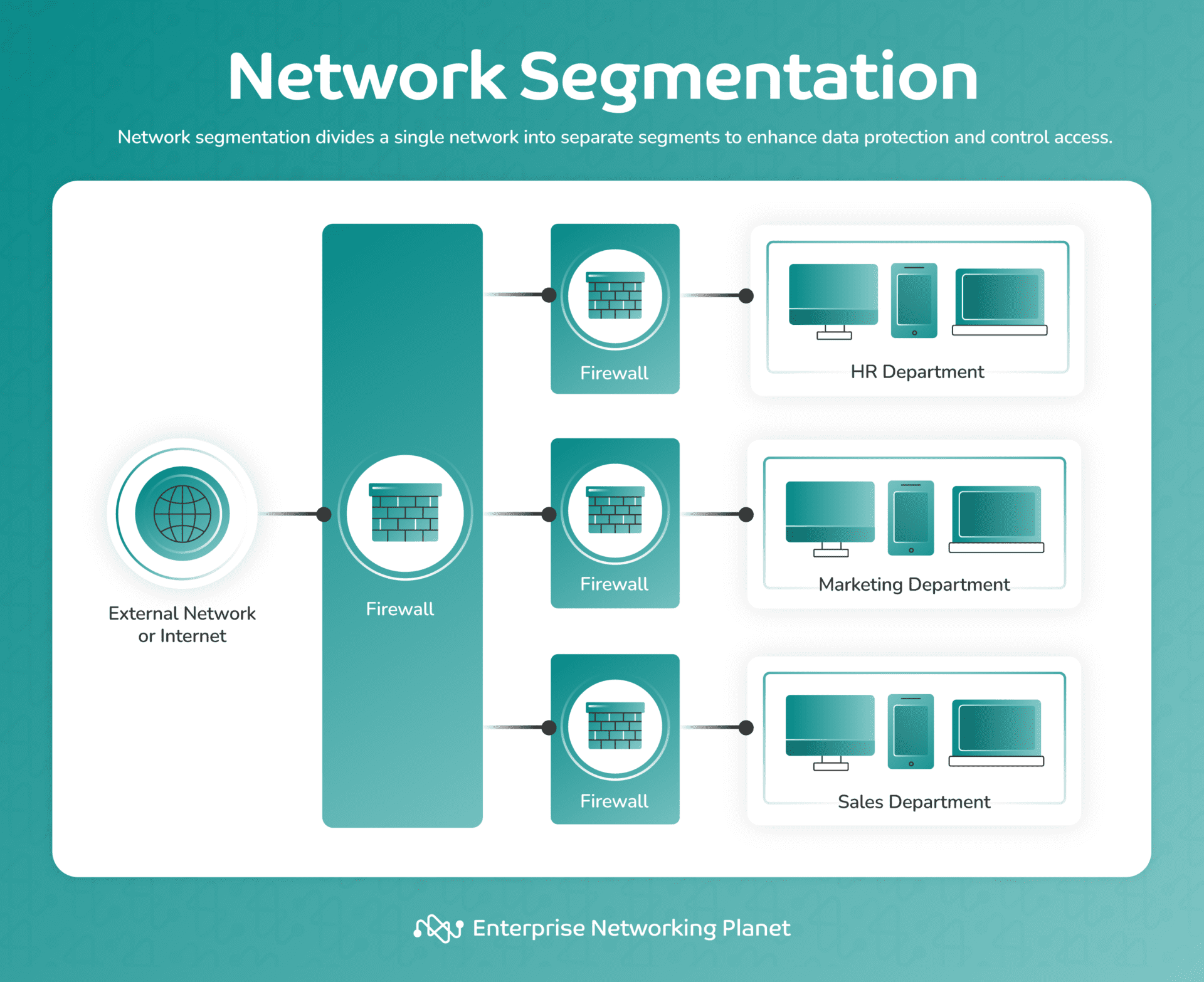
- Secure your campus network with LAN segmentation (VLANs, Micro-segmentation) and NAC deployment best practices for visibility, policy control, and Zero Trust.
- Network access control (NAC) solutions check enrollment and compliance for devices with Intune. NAC includes certain behaviors and works with Conditional Access.
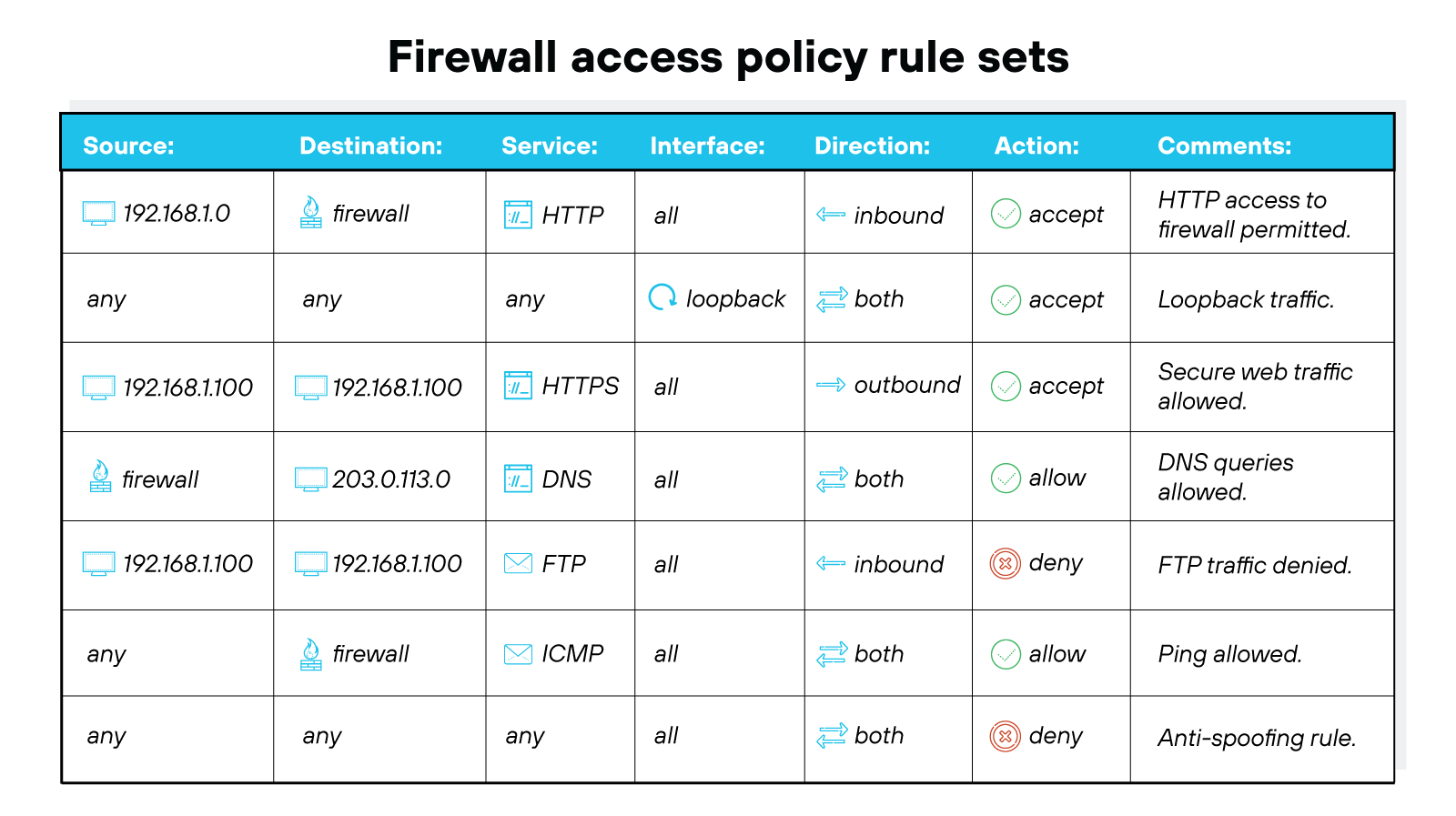
- Properly configuring these servers provides an authoritative source for managing and monitoring access, improves consistency of access control, reduces configuration maintenance, and controls access and compliance.
- Using the IEEE 802.1X standard, port-based network access control (PNAC) improves security and simplifies network administration, making it a crucial component of any organization's security strategy.
- Zero Network Changes. Zero Integration. Geni's network access control (NAC) enables practical security compliance by providing real-time visibility into all network-connected assets, ensuring they adhere to your IT security policies.
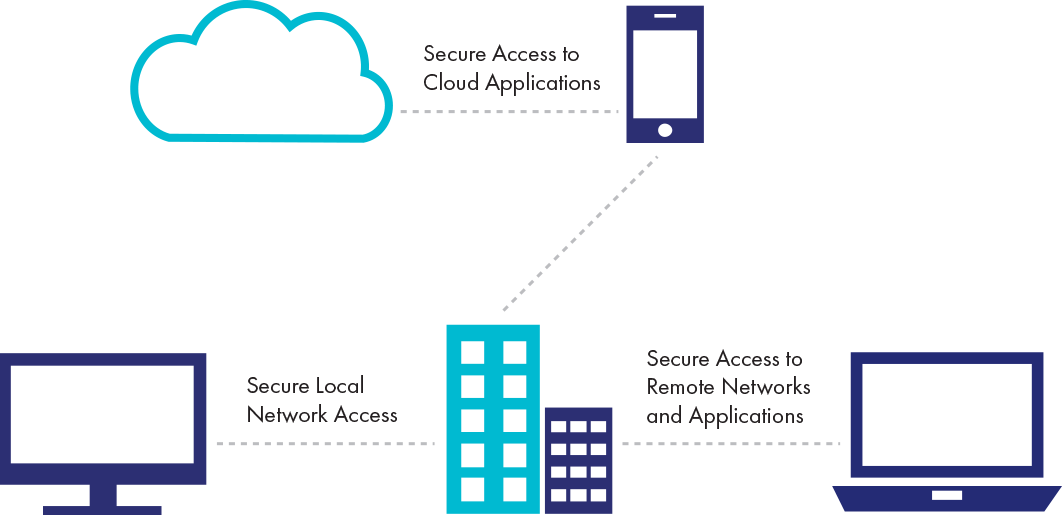
- The result was an architecture that is rigid, operationally complex, and increasingly a barrier to digital transformation. Zscaler Zero Trust Network Access (ZTNA) eliminates this outdated model entirely, replacing it with a cloud-native platform where business policies — not network location — determine who can access what, from anywhere.
- Mitigation techniques include using segmentation, access control, configuration enforcement, hardening, isolation, and patching.
- Use EDS files with network configuration tools to help you identify products and easily commission them on a network. Use our Product Compatibility Download Center or our EPS library to search for the EDS files.